
Post by : Anis Karim
Daily, billions engage in personal conversations without a second thought. Topics ranging from health to finances traverse glowing screens, guided by apps that assure users of their safety with jargon that sounds reassuring. One term frequently highlighted is “end-to-end encryption.”
This concept appears formidable and comforting. However, most users fail to grasp that encryption isn’t synonymous with complete security. It doesn’t provide invisibility, legal immunity, or an unyielding barrier against threats.
Rather, end-to-end encryption is a robust tool, but its capabilities have limits.
In an era where privacy is priceless, understanding the true implications of this concept becomes vital. While the technology safeguards messages during transit, it doesn’t necessarily shield you.
Let’s clarify what end-to-end encryption can and cannot achieve, along with the common misconceptions surrounding its effectiveness.
End-to-end encryption denotes the process of converting your message into unreadable code before it exits your device, remaining encrypted until it arrives at the recipient’s device.
Only the sender and the intended receiver possess access to the message:
Not the app.
Not the service provider.
Not potential hackers.
Not even internet service providers.
Ideally.
Visualize placing a letter inside a secure box, locking it, and sending it. The delivery person carries the sealed box but cannot open it; only the recipient with the correct key can unlock it.
This encapsulates the basic principle behind encryption.
When you dispatch a message, numerous behind-the-scenes operations occur:
Your message undergoes mathematical transformation using a key. Without this key, it is rendered as random data.
The encrypted message traverses various networks and servers in an unreadable format.
The receiver's device utilizes a digital key to revert the scrambled message back to its readable form.
During its journey, no one can intercept and interpret it as plain text.
That's the commitment.
Numerous widely-used applications tout end-to-end encryption, such as WhatsApp, Signal, and features embedded in Apple and Google devices.
Each software adopts varied implementations of encryption. Some default to protected chats, while others allow users to opt for encrypted exchanges.
Encryption doesn’t simply act as an on/off switch; it spans a range of security options.
Encryption proves effective against certain threats.
Your messages remain unreadable to hackers monitoring Wi-Fi networks.
Internet service providers cannot inspect the contents of your messages.
Apps themselves cannot access the text of encrypted conversations.
Massive data breaches from servers do not directly compromise message content.
Consequently, encryption plays a crucial role in preserving speech and privacy.
Misunderstandings often crop up here.
While encryption safeguards your messages in transit, it fails to protect against:
• Unauthorized access to your unlocked phone
• Malware on your device
• Spyware that collects your screen activity
• Applications with questionable permissions
• Keyloggers or screen capture software
If your device is compromised, encryption loses its significance.
Because messages are visible on your display.
Numerous users back up chat histories on cloud platforms.
This is where encryption might fail.
Unless encryption for backups is explicitly stated, authorities or malicious entities can access stored chats, even if they cannot read messages in real-time.
Encryption secures content only, not the context.
Data including:
• Who you communicate with
• When you send messages
• Frequency of messages
• Your location
• Device type used
This information is logged.
Metadata can reveal behavior patterns even without inspecting message contents.
In intelligence assessments, metadata can often be more insightful than the messages themselves.
Anyone can take a screenshot of a message.
Encryption doesn’t prevent forwarding.
It doesn’t erase evidence.
If the recipient chooses to save or share the content, privacy can vanish in an instant.
No encryption system operates in a vacuum devoid of human activity.
An impeccably encrypted application is futile if:
• Users fall victim to scams
• Partners misuse their access
• Friends betray trust
• Accounts are hacked
• Passwords are reused
• Devices are irresponsibly shared
Security falters when behavior disregards risk.
Governments frequently express concerns about encryption.
Why?
Because encrypted messages obstruct surveillance.
Authorities contend that criminals exploit private platforms for illicit activities.
Conversely, privacy advocates assert that encryption safeguards ordinary citizens.
Both perspectives coexist.
Encryption itself is neutral.
How it's utilized isn't.
Directly? Rarely.
Indirectly? Often.
They might:
• Request encrypted backups
• Target devices rather than servers
• Access account information
• Monitor metadata
• Employ spyware
• Obtain user credentials
The encryption appears strongest on paper.
In practice, individuals become the targets — not the algorithms.
Trust drives engagement.
Encryption has evolved into:
• A marketing advantage
• A competitive edge
• A privacy assurance
• A shield for reputation
Heightened claims of privacy attract more users.
However, no company can dictate how users act thereafter.
Language surrounding security provides comfort.
Yet absolute safety is an unreachable ideal online.
Encryption complicates breaches but doesn’t eliminate them.
It merely slows down the process.
No, it varies.
Certain apps:
• Offer full encryption
• Do not retain message content
• Limit metadata collection
Others:
• Log user activities
• Store backup data
• Share insights with partners
• Retain transaction records
“Encrypted” does not equate to “private”.
Always verify what additional data is collected.
Truth: Anyone who accesses your device can.
Truth: Metadata speaks volumes.
Truth: Security cannot substitute for sound judgment.
Truth: They nullify encryption entirely.
Truth: It never has.
Encryption is merely a layer, not an entire measure.
Biometric locks offer your first line of defense.
Theft of accounts negates encryption.
Many applications track your behavior unnecessarily.
Cloud configurations often neglect security measures by default.
Encryption is formidable, yet side channels remain.
Digital footprints never fade.
Certain apps claim to offer self-erasing messages.
This doesn't assure complete deletion.
Recipients can:
• Capture screens
• Utilize alternate devices
• Preserve images
• Export their chats
“Vanishing” typically implies disappearing publicly, not privately.
Crucial for:
• Journalists
• Activists
• Whistleblowers
• Political dissidents
• Victims of domestic violence
• Corporate investigators
• Advocates for privacy
It can be a matter of life and death.
For everyday conversations, it safeguards dignity.
Many parents assume encryption offers safety for kids.
Yet, encryption merely conceals actions—it doesn’t assure security.
Children should have:
• Education
• Oversight
• Transparent dialogue
• Digital awareness
Privacy without knowledge cultivates danger.
It secures information.
Not choices.
It guarantees safe transit.
Not relationships.
It conceals content.
Not the results of actions.
Encryption will fortify over time.
However, surveillance tactics will advance as well.
This isn’t a rivalry someone ‘wins’.
It’s an ongoing competition.
Privacy will always be a temporary state.
End-to-end encryption is a remarkable innovation.
It defends expression in an era marked by surveillance.
It fosters liberty in oppressive environments.
It provides dignity in the digital realm.
Yet, it isn’t magical.
It doesn’t eradicate recklessness.
It doesn’t halt screenshots.
It doesn’t shield emotions.
It doesn’t guard against poor choices.
Encryption ensures message safety.
Wisdom safeguards lives.
And in the digital landscape —
Wisdom is the most formidable password you can create.
This article is for informational purposes only and does not serve as legal, cybersecurity, or technical advice. Readers should seek guidance from qualified professionals for personal data protection strategies.

US Stocks Slide as AI Fears, Inflation and Oil Surge Weigh
US stocks dropped as AI disruption fears hit tech firms, inflation rose above forecasts, and oil pri

Pacific Prime Wins Top Honors at Cigna Awards 2026
Pacific Prime secured Top Individual Broker and Top SME Broker awards at Cigna’s Annual Broker Award

QatarEnergy Halts LNG Output After Military Attack
QatarEnergy has stopped LNG production after military attacks hit its facilities in Ras Laffan and M
Strong 6.1 Magnitude Earthquake Hits West Sumatra, No Damage
A 6.1 earthquake struck off West Sumatra, Indonesia. No casualties, damage, or tsunami alert reporte

Saudi Confirms Drone Strike on US Embassy Riyadh
Two drones hit the US Embassy in Riyadh, causing a small fire and minor damage. No injuries were rep

UAE Restarts Limited Flights as Regional Airspace Disruptions Continue
UAE restarts limited flights from Dubai as US-Israel attacks on Iran disrupt regional airspace, forc

Asia Faces Energy Shock After Iran Closes Strait
Iran shuts Strait of Hormuz amid US-Israel strikes, sending oil prices higher and raising serious en

Bank of Baroda Faces Abu Dhabi Legal Battle over NMC Collapse
Bank of Baroda’s involvement in Abu Dhabi litigation tied to the NMC Healthcare collapse raises repu
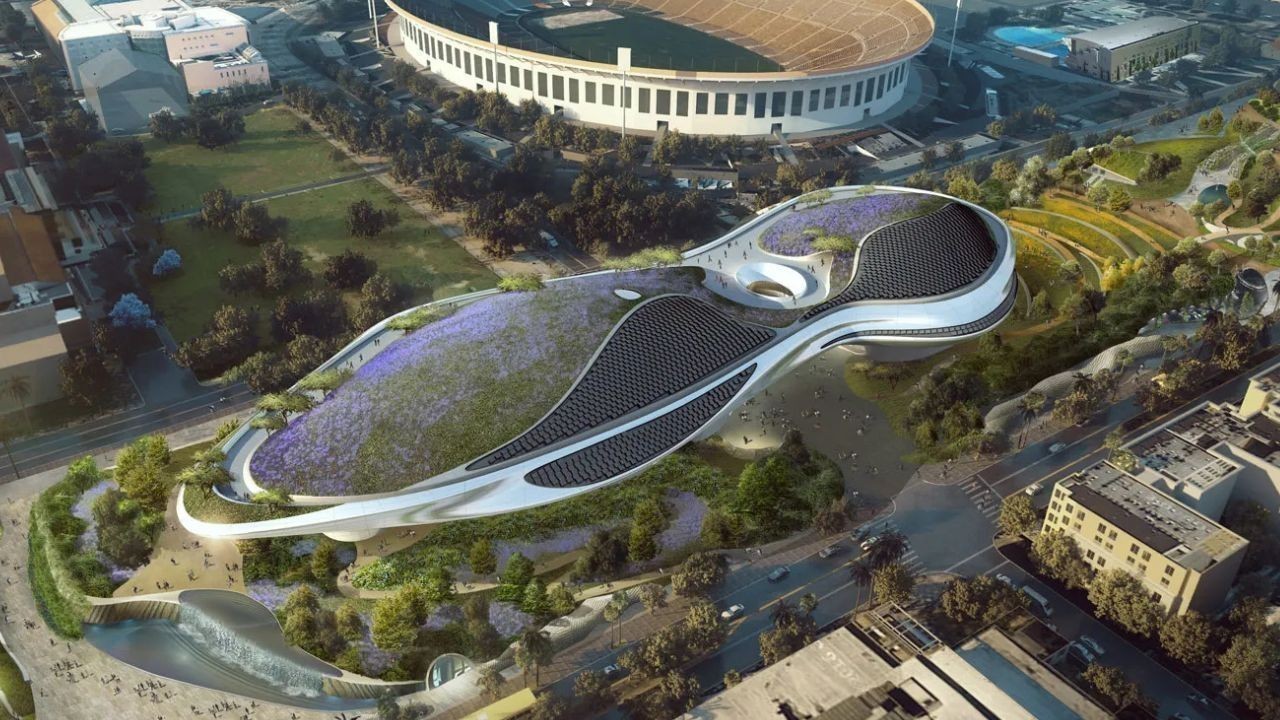
Top Museum Openings of 2026 Set to Transform Global Tourism
From Los Angeles to Abu Dhabi and Brussels, 2026 brings major museum launches—Lucas Museum, Guggenhe

UAE Tour Highlights UAE’s Strength in Hosting Global Sports Events
Abu Dhabi Sports Council says the successful UAE Tour reflects the UAE’s leading role in hosting maj

EU Seeks Clarity from US After Supreme Court IEEPA Ruling
European Commission urges full transparency from the US on steps after Supreme Court ruling, emphasi

SpaceX Launches 53 New Satellites for Expanding Starlink Network
SpaceX launches 53 Starlink satellites in two Falcon 9 missions, breaking reuse records and expandin

RTA Awards Contract for Phase II of Hessa Street Upgrade in Dubai
Phase II of Hessa Street Development to add bridges, tunnel, and upgraded intersections, doubling ca

UAE Gold Prices Today, Monday 16 February 2026: Dubai & Abu Dhabi Updated Rates
Gold prices in UAE on 16 Feb 2026 updated: 24K around AED 599.75/gm, 22K AED 555.25/gm, and 18K AED

Over 25 Ahmedabad Schools Receive Bomb Threat Email, Authorities Investigate
More than 25 schools in Ahmedabad evacuated after bomb threat emails mentioning Khalistan. Authoriti