Post by : Anis Karim
Losing a smartphone has evolved beyond a mere inconvenience; it can represent an invasion of privacy, financial despair, and a loss of irreplaceable memories. Hence, anti-theft applications have become increasingly popular, claiming to provide peace of mind by offering tracking, locking, and remote data deletion. As our reliance on technology deepens, these tools have emerged as essential players in safeguarding digital lives.
At first glance, these apps seem invaluable. They promise to locate lost devices, disable stolen ones, and eliminate sensitive data before it falls into the wrong hands. Families employ these features to keep track of children, while businesses utilize them to secure company smartphones.
However, what appears to serve as a protective measure may also open doors to unwanted surveillance. The same application facilitating device tracking can potentially monitor user movements. In this complicated ecosystem, distinguishing protection from intrusion can be difficult for many.
As the capabilities of anti-theft solutions expand, users find themselves grappling with an essential dilemma: Do these applications safeguard privacy or do they encroach upon it?
Understanding the inner workings of these applications is crucial for identifying potential risks.
Anti-theft applications predominantly depend on GPS and internet functionality to trace devices. When activated, these services consistently communicate the phone’s location to the user.
While you might see a simple map on your screen, behind the scenes, your location data is being collected and processed by the app’s providers.
The core functions of anti-theft applications include:
Locking devices
Deleting files
Flashing screens
Sounding alarms
Disabling SIM cards
Monitoring activities
Taking photos
Activating microphones
Utilizing these features necessitates in-depth permissions, making the app integral to the phone’s operation.
To use these applications, users typically register via email or phone numbers, creating profiles that may retain device-related data, including location histories.
Consequently, physical presence translates into digital information.
There's a clear rationale for the widespread trust in these applications.
The emotional fallout from a lost or stolen phone is significant. People fear strangers accessing private content. These apps provide a semblance of control amid chaos.
Parents frequently depend on tracking features to keep tabs on children, while families exchange real-time location info. Such practices have normalized surveillance under the guise of assurance.
Many companies mandate the installation of tracking applications on company devices, justifying this under the banner of security.
While these apps promise safety, they often come with a cost—your privacy.
Numerous applications solicit permission to access:
Location continuously
Contacts
SMS
Photos
Microphone
Camera
Storage
Call logs
Network access
In moments of urgency, users often grant access without fully understanding its implications.
Your data may be stored across:
Corporate servers
Cloud systems
Partner networks
Third-party data centers
Few users comprehend:
How long their data will be stored
Who is permitted access
If it is encrypted
If it is shared or sold
The legalities surrounding data sharing
Privacy policies are frequently extensive and confusing, often going unread.
Surveillance may take on many forms beyond clear observation.
Your tracking data can disclose:
Residential geographic areas
Work locations
Recreation spots
Social circles
Daily routines
Personal habits
Thus, location data transcends mere geographical tracking; it offers insights into your behavior.
While tracking lost devices is practical, tracking individuals without their awareness poses ethical dilemmas.
Tools designed for safety can unintentionally enable abuse.
In some cases, anti-theft applications have been exploited to monitor unsuspecting partners in toxic relationships.
Remote access opens avenues for unwanted observation, leading to discomfort among employees.
The ability to remotely lock devices can instigate control by abusive partners.
Technology can alter the dynamics of relationships.
Not all anti-theft applications hold the same safety standards.
Reliable apps should clearly communicate:
Data collection specifics
Storage methods
Access permission
Data retention duration
Data sharing practices
A lack of clarity indicates potential risk.
Quality apps solicit only the necessary permissions. Unjustified requests for excessive access should raise concerns.
Apps that store information locally mitigate exposure, while cloud-based systems raise vulnerabilities.
While privacy laws are in place, enforcement remains inconsistent.
Just agreeing to terms does not guarantee meaningful understanding.
Even the most secure systems are not infallible; when breaches occur, personal data becomes vulnerable.
Once data is transferred to a third-party database, reclaiming it proves challenging.
Free services often come with a hidden cost—your personal data.
Location information can be leveraged for profit. Analyzing behavior patterns attracts advertisers, while device histories serve data analytics firms' interests.
Many firms do not disclose the monetary benefits derived from user data, yet partnerships and anonymization can still yield profits.
Ironically, tools meant for safety can also compromise it.
Users seldom have visibility into:
Data access history
Time of access
Purpose of access
This hidden processing obscures the concept of privacy.
Users may lean heavily on protective technology rather than adopting preventive behaviors.
Signs of potentially unsafe applications include:
Excessive permission requests
Absence of clear policies
Ambiguous explanations for data use
Mandatory account creation
No options for deletion
No claims of encryption
Hidden functionalities
If the app's data practices are unclear, it is likely excessive.
Awareness serves as your best defense.
Only grant access that is absolutely necessary, and if feasible, restrict background activity.
Review permissions periodically, eliminating unnecessary access.
Utilizing multiple apps elevates risks.
Integrated solutions provide more effective security management.
Educate loved ones on distinguishing safety from surveillance.
Absolute safety is a myth.
Striving for equilibrium is the more realistic goal.
Individuals must contemplate their compromises:
Convenience for privacy
Protection for exposure
Speed for safety
There are no one-size-fits-all answers.
These applications are expected to evolve significantly.
Future innovations may include behavior prediction, pattern detection, and anomaly alerts—improving device recovery but also enhancing monitoring.
Biometric authentication could replace traditional passwords, but vulnerability remains since biometric data, once compromised, is irreplaceable.
Future technological advancements may result in continuous, automated tracking, obscuring the line between safety and surveillance.
Before installing an anti-theft app, pose these questions:
Who handles your data?
Where does it go?
Can it be deleted?
Is access controllable?
Does it emphasize safety over control?
Let mindfulness dictate your choices, not fear.
Anti-theft applications serve as neither heroes nor villains; they are reflections of their users' intent. These tools carry the ability to both protect and surveil.
Ultimately, morality is not determined by technology, but by those who wield it.
In embracing technology that pervades our lives, ensuring our methods do not compromise our freedom is vital. Genuine digital safety emerges from comprehending technology, not merely employing it.
A truly secure device is one that is both understood and respected.
This article serves to inform; it is not a substitute for legal or cybersecurity expertise. Readers should independently verify app policies and consult experts for data protection and security queries.

US Stocks Slide as AI Fears, Inflation and Oil Surge Weigh
US stocks dropped as AI disruption fears hit tech firms, inflation rose above forecasts, and oil pri

Pacific Prime Wins Top Honors at Cigna Awards 2026
Pacific Prime secured Top Individual Broker and Top SME Broker awards at Cigna’s Annual Broker Award

QatarEnergy Halts LNG Output After Military Attack
QatarEnergy has stopped LNG production after military attacks hit its facilities in Ras Laffan and M
Strong 6.1 Magnitude Earthquake Hits West Sumatra, No Damage
A 6.1 earthquake struck off West Sumatra, Indonesia. No casualties, damage, or tsunami alert reporte

Saudi Confirms Drone Strike on US Embassy Riyadh
Two drones hit the US Embassy in Riyadh, causing a small fire and minor damage. No injuries were rep

UAE Restarts Limited Flights as Regional Airspace Disruptions Continue
UAE restarts limited flights from Dubai as US-Israel attacks on Iran disrupt regional airspace, forc

Asia Faces Energy Shock After Iran Closes Strait
Iran shuts Strait of Hormuz amid US-Israel strikes, sending oil prices higher and raising serious en

Bank of Baroda Faces Abu Dhabi Legal Battle over NMC Collapse
Bank of Baroda’s involvement in Abu Dhabi litigation tied to the NMC Healthcare collapse raises repu
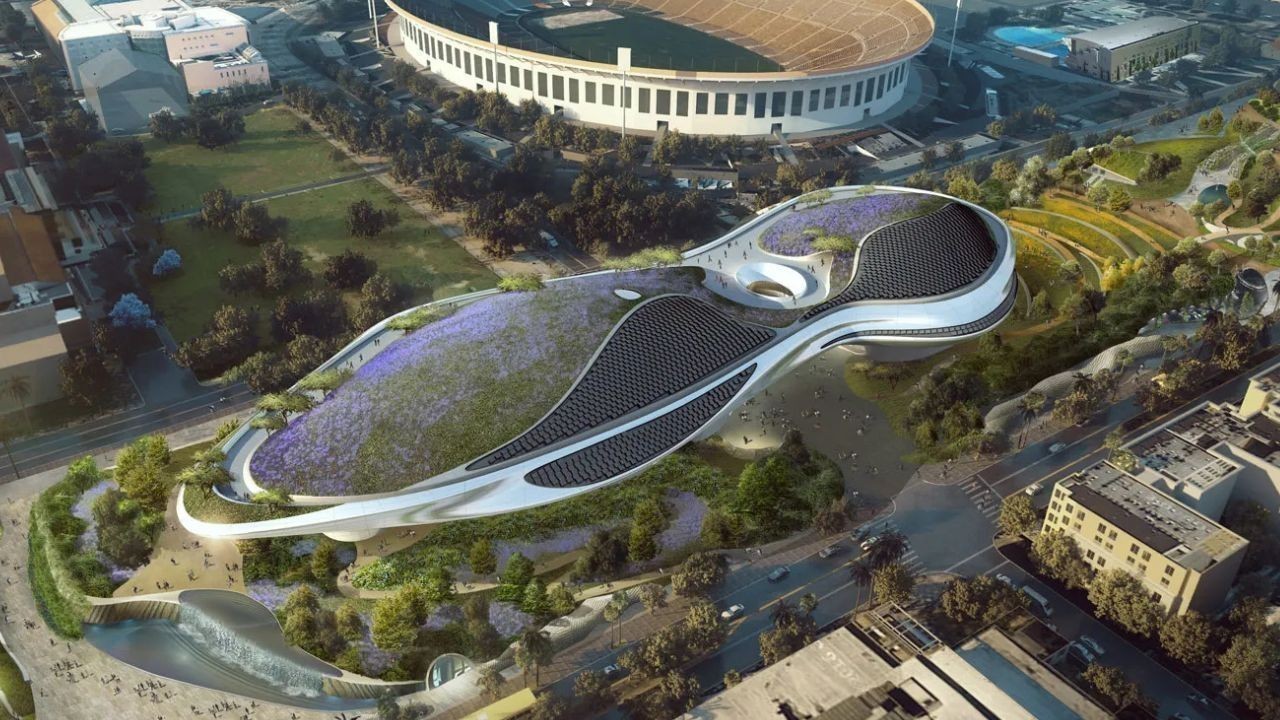
Top Museum Openings of 2026 Set to Transform Global Tourism
From Los Angeles to Abu Dhabi and Brussels, 2026 brings major museum launches—Lucas Museum, Guggenhe

UAE Tour Highlights UAE’s Strength in Hosting Global Sports Events
Abu Dhabi Sports Council says the successful UAE Tour reflects the UAE’s leading role in hosting maj

EU Seeks Clarity from US After Supreme Court IEEPA Ruling
European Commission urges full transparency from the US on steps after Supreme Court ruling, emphasi

SpaceX Launches 53 New Satellites for Expanding Starlink Network
SpaceX launches 53 Starlink satellites in two Falcon 9 missions, breaking reuse records and expandin

RTA Awards Contract for Phase II of Hessa Street Upgrade in Dubai
Phase II of Hessa Street Development to add bridges, tunnel, and upgraded intersections, doubling ca

UAE Gold Prices Today, Monday 16 February 2026: Dubai & Abu Dhabi Updated Rates
Gold prices in UAE on 16 Feb 2026 updated: 24K around AED 599.75/gm, 22K AED 555.25/gm, and 18K AED

Over 25 Ahmedabad Schools Receive Bomb Threat Email, Authorities Investigate
More than 25 schools in Ahmedabad evacuated after bomb threat emails mentioning Khalistan. Authoriti